Install a new MIT KDC
The following gives a very high level description of the KDC installation process. To get more information see specific Operating Systems documentation, such as RHEL documentation, CentOS documentation, or SLES documentation.
![[Note]](http://docs.hortonworks.com/HDPDocuments/Ambari-2.1.1.0/bk_Ambari_Security_Guide/common/images/admon/note.png) |
Note |
|---|---|
| Because Kerberos is a time-sensitive protocol, all hosts in the realm must be time-synchronized, for example, by using the Network Time Protocol (NTP). If the local system time of a client differs from that of the KDC by as little as 5 minutes (the default), the client will not be able to authenticate. |
Install the KDC Server
- Install a new version of the KDC server:
RHEL/CentOS/Oracle Linux
yum install krb5-server krb5-libs krb5-workstationSLESzypper install krb5 krb5-server krb5-client - Using a text editor, open the KDC server configuration file, located by default here:
vi /etc/krb5.conf - Change the [realms] section of this file by replacing the default “kerberos.example.com” setting for the kdc and admin_server properties with the Fully Qualified Domain Name of the KDC server host. In the following example, “kerberos.example.com” has been replaced with “my.kdc.server”.
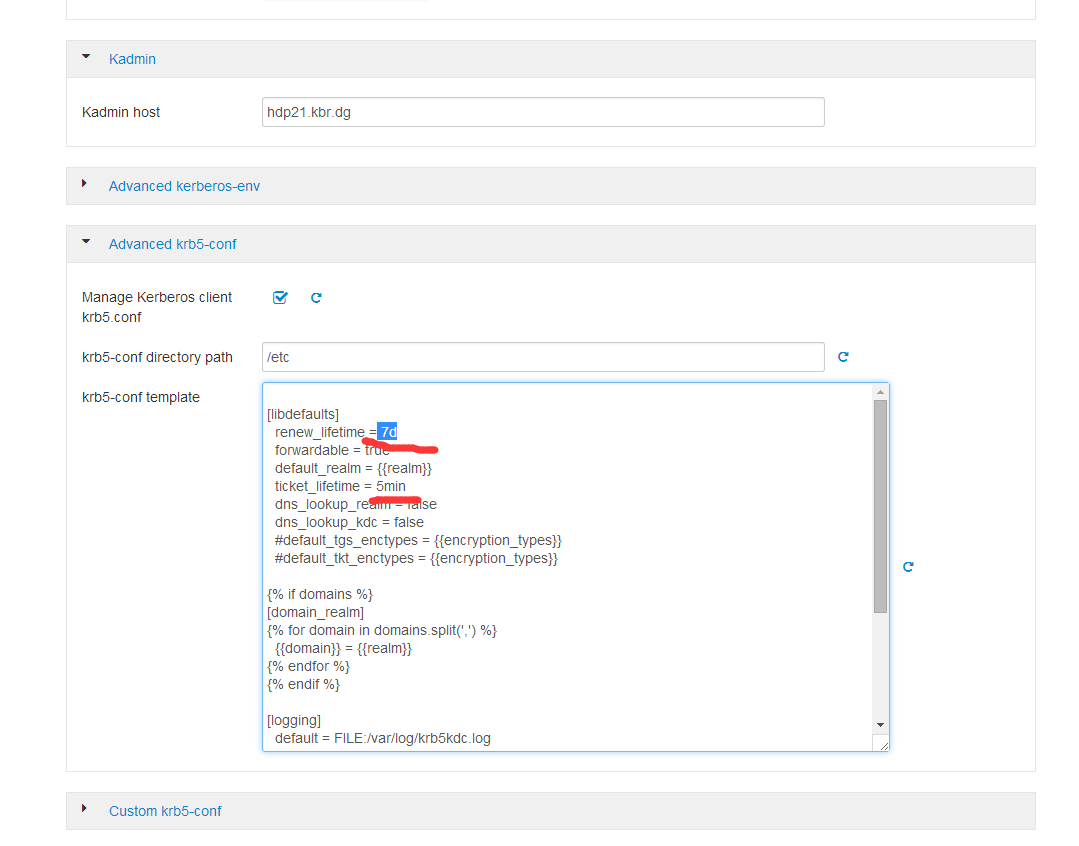
[realms] EXAMPLE.COM = { kdc = my.kdc.server admin_server = my.kdc.server } - Some components such as HUE require renewable tickets. To configure MIT KDC to support them, ensure the following settings are specified in the
libdefaultssection of the/etc/krb5.conffile.renew_lifetime = 7d
Create the Kerberos Database
- Use the utility kdb5_util to create the Kerberos database.
RHEL/CentOS/Oracle Linux
kdb5_util create -sSLESkdb5_util create -s
Start the KDC
- Start the KDC server and the KDC admin server.
RHEL/CentOS/Oracle Linux 6
/etc/rc.d/init.d/krb5kdc start/etc/rc.d/init.d/kadmin startRHEL/CentOS/Oracle Linux 7systemctl start krb5kdcsystemctl start kadminSLES 11rckrb5kdc startrckadmind start![[Important]](http://docs.hortonworks.com/HDPDocuments/Ambari-2.1.1.0/bk_Ambari_Security_Guide/common/images/admon/important.png)
Important When installing and managing your own MIT KDC, it is very important to set up the KDC server to auto-start on boot. For example: RHEL/CentOS/Oracle Linux 6
chkconfig krb5kdc onchkconfig kadmin onRHEL/CentOS/Oracle Linux 7
systemctl enable krb5kdcsystemctl enable kadminSLES 11
chkconfig rckrb5kdc onchkconfig rckadmind on
Create a Kerberos Admin
Kerberos principals can be created either on the KDC machine itself or through the network, using an “admin” principal. The following instructions assume you are using the KDC machine and using the kadmin.local command line administration utility. Using kadmin.local on the KDC machine allows you to create principals without needing to create a separate “admin” principal before you start.
![[Note]](http://docs.hortonworks.com/HDPDocuments/Ambari-2.1.1.0/bk_Ambari_Security_Guide/common/images/admon/note.png) |
Note |
|---|---|
| You will need to provide these admin account credentials to Ambari when enabling Kerberos. This allows Ambari to connect to the KDC, create the cluster principals and generate the keytabs. |
- Create a KDC admin by creating an admin principal.
kadmin.local -q "addprinc admin/admin" - Confirm that this admin principal has permissions in the KDC ACL. Using a text editor, open the KDC ACL file:
RHEL/CentOS/Oracle Linux
vi /var/kerberos/krb5kdc/kadm5.acl
SLES
vi /var/lib/kerberos/krb5kdc/kadm5.acl - Ensure that the KDC ACL file includes an entry so to allow the admin principal to administer the KDC for your specific realm. When using a realm that is different than EXAMPLE.COM, be sure there is an entry for the realm you are using. If not present, principal creation will fail. For example, for an admin/admin@HADOOP.COM principal, you should have an entry:
*/admin@HADOOP.COM * - After editing and saving the kadm5.acl file, you must restart the kadmin process.
RHEL/CentOS/Oracle Linux 6
/etc/rc.d/init.d/kadmin restart
RHEL/CentOS/Oracle Linux 7
systemctl restart kadmin
SLES 11
rckadmind restart
Install the JCE
- On the Ambari Server, obtain the JCE policy file appropriate for the JDK version in your cluster.
- For Oracle JDK 1.8:http://www.oracle.com/technetwork/java/javase/downloads/jce8-download-2133166.html
- For Oracle JDK 1.7:http://www.oracle.com/technetwork/java/javase/downloads/jce-7-download-432124.html
wget http://dl.huangshiyang.com/UnlimitedJCEPolicyJDK7.zip
- Save the policy file archive in a temporary location.
- On Ambari Server and on each host in the cluster, add the unlimited security policy JCE jars to
$JAVA_HOME/jre/lib/security/.For example, run the following to extract the policy jars into the JDK installed on your host:unzip -o -j -q UnlimitedJCEPolicyJDK7.zip -d /usr/jdk64/jdk1.7.0_67/jre/lib/security/
- Restart Ambari Server.
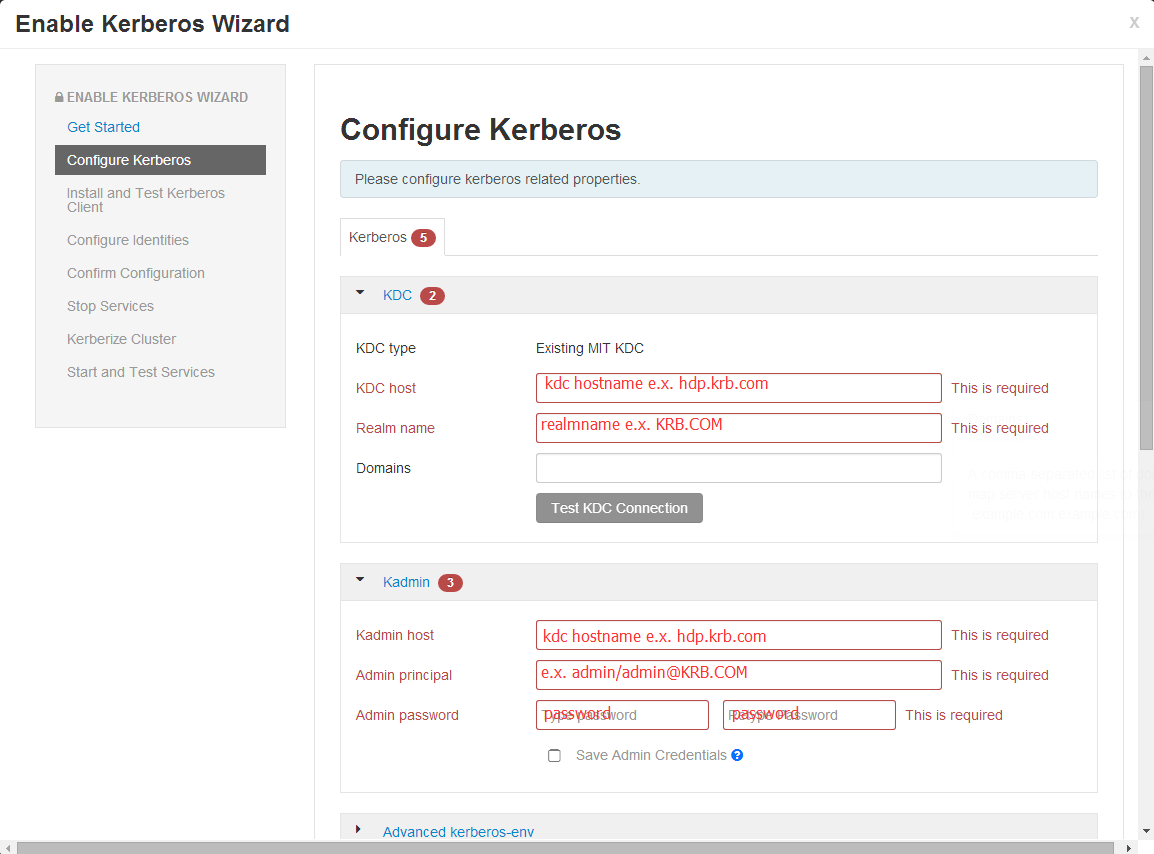
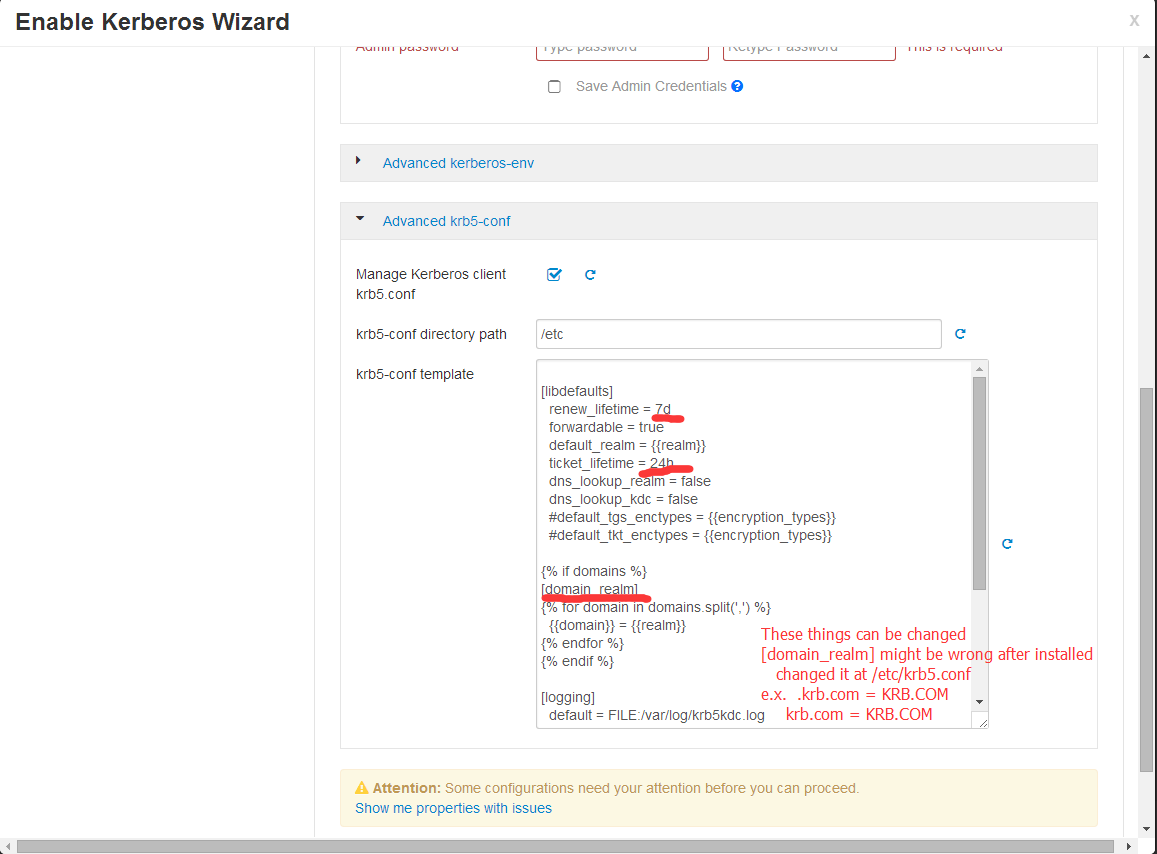
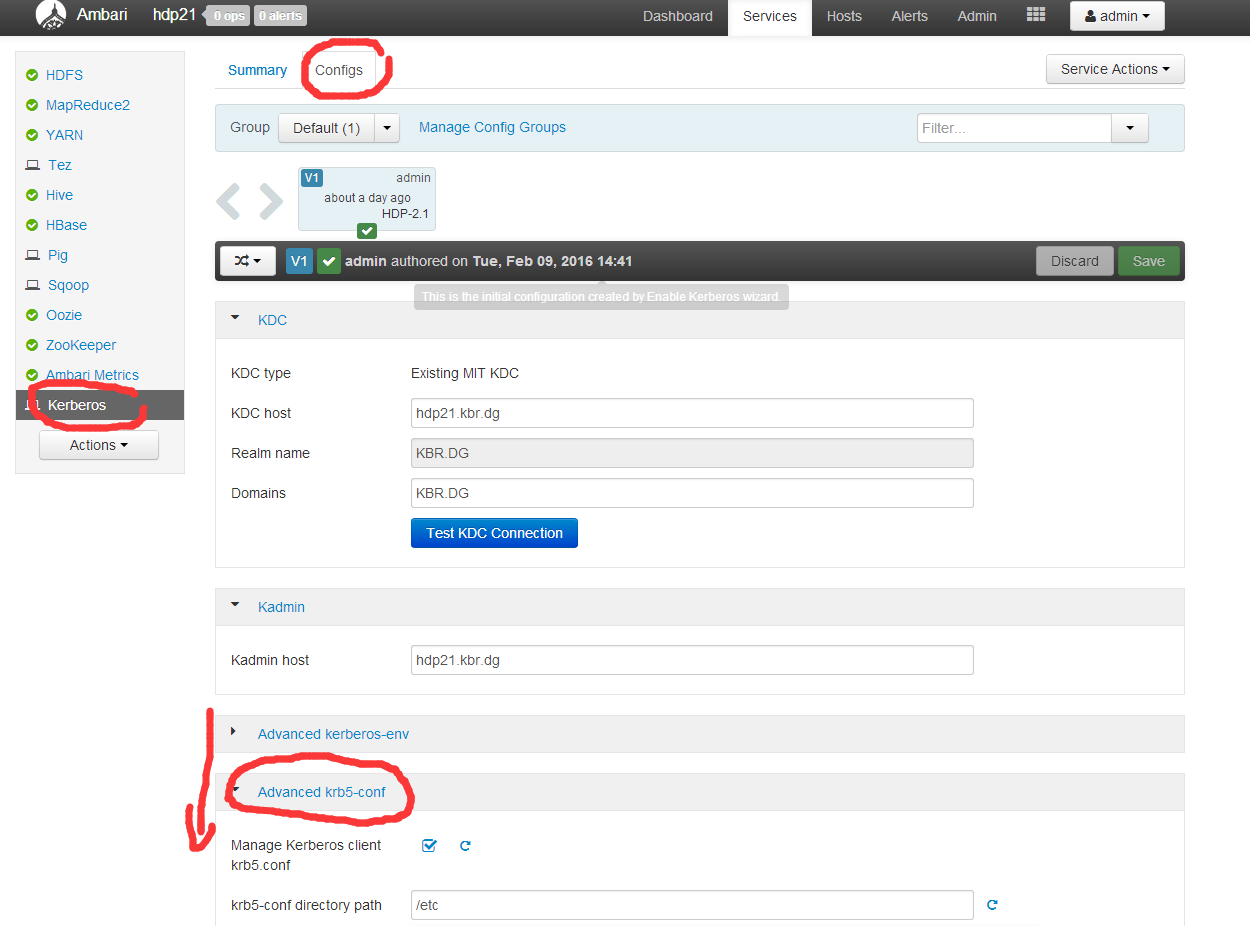
- Proceed to Running the Security Wizard.
wget http://dl.huangshiyang.com/UnlimitedJCEPolicyJDK7.zip unzip -o -j -q UnlimitedJCEPolicyJDK7.zip -d /usr/jdk64/jdk1.7.0_67/jre/lib/security/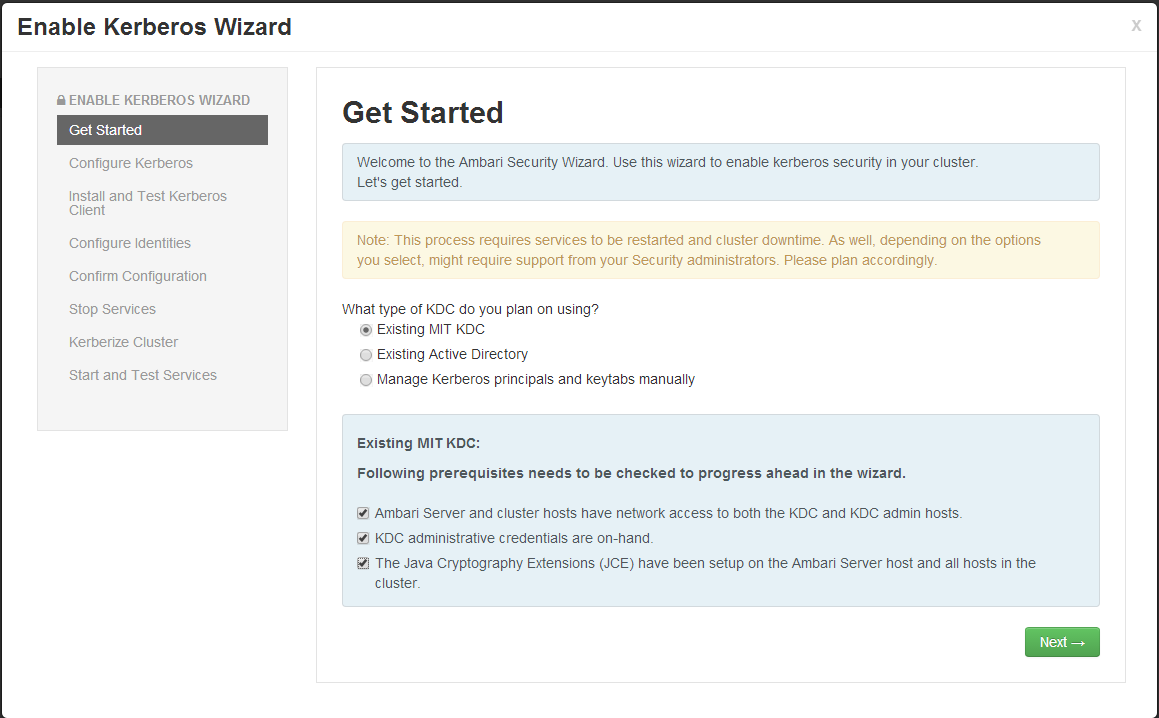
I know it is hard to write articles manually everyday,
but there is solution for this. Just search in google for;
servitu’s tricks